Dealing With The Two Facets Of Vulnerability Analysis
Comprehending the risk factors and prevailing threats in the IT environment has become a necessary prowess to achieve in the present day aura of business. Underestimating or avoiding these prospects could possibly lead your firm into tremendous debacle. Vulnerability Analysis is timely process of probing and scrutinizing the vulnerable and assailable weaknesses in your computer system. This aids us to examine and improvise system security stratagem, design or any other related internal controls and indeed induce a better one.
There are 2 major facets which one needs to deal with amid implementing vulnerability analysis.
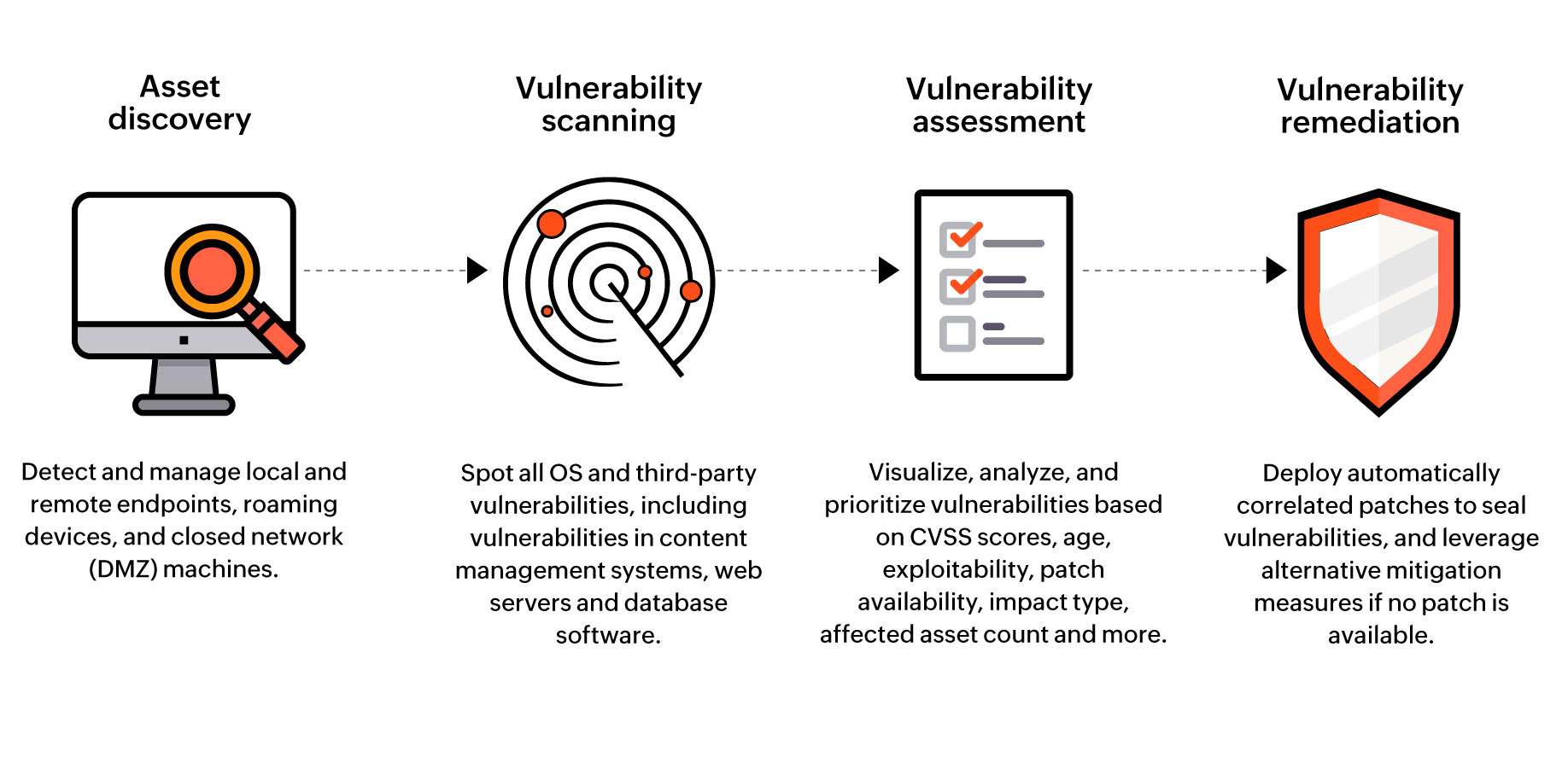
Vulnerability Assessment
This assessment typically bestows deep insights on what vulnerabilities exist which mainly are known software weaknesses. It detects when the equipment could be ventured and is mainly performed by in-house staff focusing on breadth over depth. It entails usage programmed network security scanning tools. It is advised to execute it quarterly principally if a new device is loaded. Ideally, a vulnerability report must consist of title, description and ferocity of the flaw unraveled.
Penetration Testing
This testing identifies what information was compromised and spots out unknown flaws in the system. Unlike the previous assessment, it behests zenith skills and operation by an independent outside service or a pet tester. It is recommended to perform this twice once or twice a year. A penetration test report should be concise and up to the point. Also it must capsulate the methodology of attack and exploit and the suggestions for improvising so that the customer gets a pristine idea.
These two fundamental methodologies sum up the vulnerability assessment explicitly .They are both requisite for a controlled security strategy .These powerfully robust tool can make a major contribution in sustaining a sceured and extemporized networking environment.